News
From Organic Design wiki
Free SSL certs for everyone!!! |
| Posted by Nad on 03 December 2015 at 19:53 |
|---|
This post has the following tags : Server
|
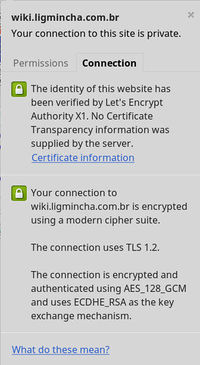
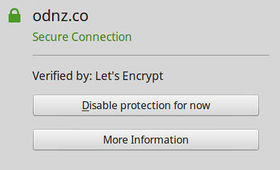
| LetsEncrypt is a new Certificate Authority, it’s free, automated, and open! It went public at 18:00 UTC today, and we had our first certificate made within the hour, and documented the procedure here.
The procedure is far simpler than all the back-and-forth of signing and requests that is required with the "legacy" corporate method, you simply install the LetsEncrypt utility on your server and tell it to make all your sites secure! Simple as that! Although we do have a very complicated configuration so I decided to have it just make the certificates and let me adjust the configuration manually - but even that process was eazy peazy lemon squeezy :-) Here's screenies of Chromium (right), Firefox and SSL labs responses to our fist test domain secured with a LetsEncrypt certificate. |